Harvey Norman, the retail giant with 13 stores in the Republic and a further two stores in Northern Ireland, has admitted to customers that it suffered a data breach through a third-party tool used on its website. “We wish to alert you to a data breach that has occurred in the systems of a third-party website service provider, Typeform, which has resulted in the unauthorised access to some Harvey Norman data,” the company said earlier this week in a statement.
How to Check If Your Business or Personal Email May Have Been Compromised
It’s 2018, and cyber crime is on the rise. It seems every other week there is another data breach or cyber attack somewhere in the world, and many people are rightfully apprehensive that they may be hacked too, or even that their details may have been exposed online through a breach of a service that they use. What if your email and password were compromised in the Adobe breach in 2013, the Yahoo breach in 2016, or the LinkedIn breach in 2012? What if your email had been obtained online and sold to cyber criminals as part of a spam list, such as Exploit.In, or the Anti Public Combo List, both discovered in 2016? If so, you may be at risk of hackers gaining access to your accounts, or even committing identity fraud against you. Luckily, security researcher and Microsoft regional director Troy Hunt has developed a database so that you can check to see if you’ve been compromised – so you can secure your online presence again.
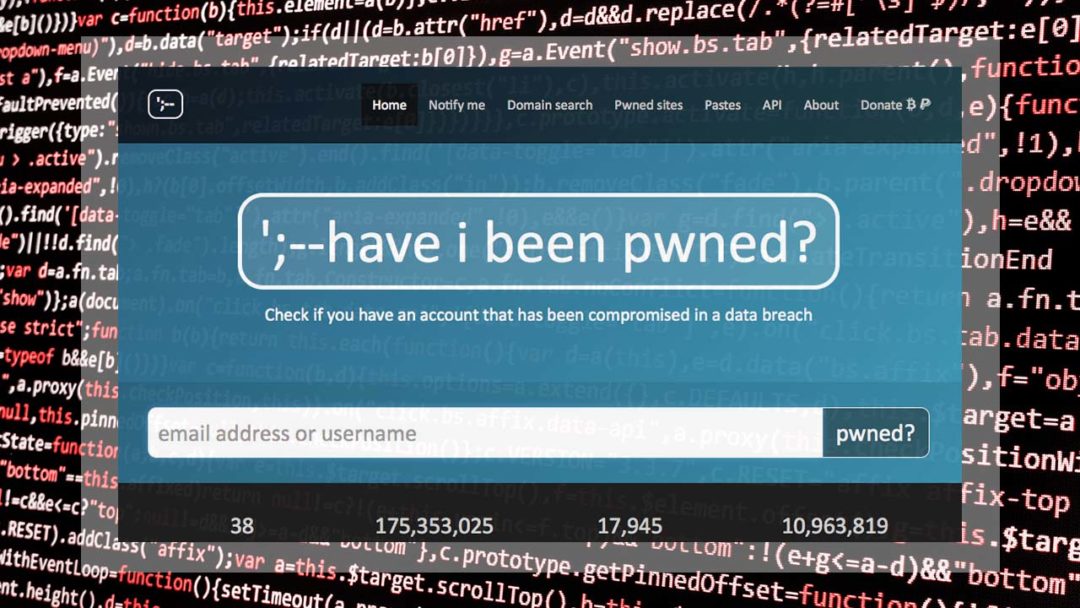
haveibeenpwned.com is a breach database run by security researcher and Microsoft regional director Troy Hunt
University of Greenwich Ordered to Pay £120,000 After Data Leak
In one of the last data breach fines to be handed down in a pre-GDPR Europe, the University of Greenwich has been ordered to pay a £120,000 fine to the Information Commissioner’s Office. The breach in question stemmed from a micro-website set up by students in 2004, and ultimately resulted in the details of 20,000 staff members and students being leaked online.

The University of Greenwich, in London, has accepted that it was responsible for the incident, and intends to pay the fine immediately.
What to Expect When the GDPR Comes Into Effect… Next Friday
Almost two years ago, the European Union signed the General Data Protection Regulation (better known as the GDPR) into law, allowing for a 24 month period before the regulation would become binding to allow organisations and businesses time to comply with its requirements. At the time of writing, the GDPR will come into force in just eight days, a thought which may strike fear into the hearts of many business owners who are not going to be fully compliant by the deadline. So what exactly is going to happen, come Friday the 25th of May? We’ve taken the time to compile some information and predictions to help cut through the noise and focus on what’s important.

The GDPR, which replaces the 1995 Data Protection Directive, was adopted on 14th April 2016 and will become enforceable on 25th May 2018.
Less Businesses Reporting Ransomware Despite Increase In Attacks
It seems that everyone in the cyber security sphere is talking about ransomware these days. Last year, attacks such as WannaCry, NotPetya and BadRabbit took the business world by storm, costing billions in damages. Ransomware is by no means a new threat (it has been around since at least 2005), but it is one of the fastest growing and most costly. Cyber crime is constantly changing, and criminals keep creating news ways to steal money. Ransomware has gotten increasingly sophisticated since 2005, but the people using and deploying it haven’t necessarily – now some cyber criminals are making more money selling high-tech ransomware strains to non-technical criminals than if they were to conduct the attacks themselves. The result is that more and more ‘hackers’ have access to ransomware and need very little technical know-how to operate it, leading to more and more ransomware attacks each year. It may come as a surprise, then, to hear that the FBI received less reports of ransomware attacks in 2017 than in 2016 and 2015, despite the increase in attacks.


