Another day, another data breach, it seems. On Friday, Quora became aware of an incident involving an “unauthorised third party” accessing data from 100 million users of the Q&A platform, and yesterday it began to notify users in an attempt to contain the incident. Quora Tweeted late last night, “We have discovered that some user data was compromised by unauthorized access to our systems. We’ve taken steps to ensure that the situation is contained and are notifying affected users. Protecting your information is our top priority” and directed users to a blog post with further information.
Identity Theft & Account Takeover Attacks on the Rise
Cyber criminals have always targeted users, finding it easier to trick unsuspecting employees than to bypass complex technical security measures – and this trend has been growing steadily the last few years. Identify fraud, where criminals impersonate someone else in order to steal their money or use their account to manipulate others, is now one of the most common types of cyber crime there is. Account takeover attacks, where criminals gain access to a user’s account and use it to send spam or phishing emails, is also on the rise, often allowing malicious emails to bypass email security filters.

Phishing remains one of the most common attack vectors for criminals – one study alarmingly found that 93% of phishing emails contained ransomware
Eir Loses Unencrypted Laptop Containing 37,000 Customers’ Details
Eir is back in hot water again with the Data Protection Commissioner after the company issued a statement stating that it had lost an unencrypted staff laptop containing the details of 37,000 Eir customers. Eir has said that the data contained names, email addresses and customer account number, but that no financial details were compromised in the breach.

Eir is no stranger to data breaches, and has reported having multiple laptops with customer data lost or stolen in the past
Ransomware Strain ‘SamSam’ Reportedly Earned Handlers Over €5.1m
A strain of ransomware titled SamSam has earned its handlers over 5.1 million euros to date, according to estimates, since it first began hitting enterprises in 2015. Security firm Sophos has released the data in a report, after tracking the Bitcoin addresses found on SamSam ransom notes and sample files.
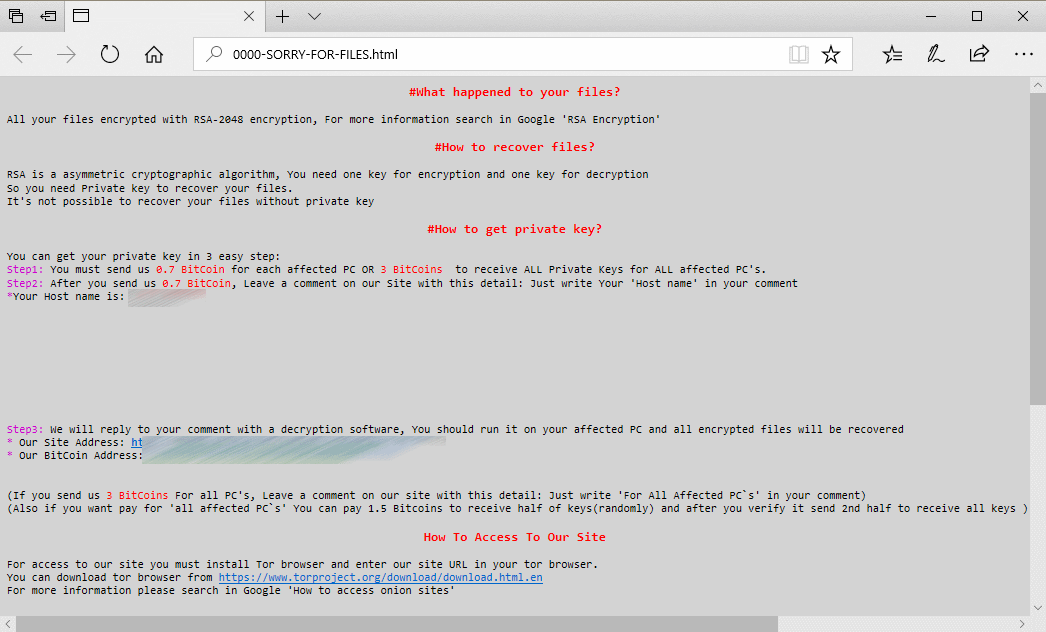
The note displayed on PCs that were infected by SamSam ransomware, as seen by businesses, hospitals, schools, local councils and more
Ticketmaster Ireland Among Those Affected in Huge Third-Party Data Breach
It has come to light that a recent breach disclosed by Ticketmaster UK may be much larger than initially reported, with not just the company’s UK site, but also their sites for Ireland, New Zealand, Australia, Turkey and even the US found to contain digital card-skimming code. Similar to the recent breach at Harvey Norman, this incident was caused by cyber criminals compromising a third-party service provider, not the site itself directly, leading security experts to believe many more websites may be at risk or have been compromised. This is part of a concerning new trend whereby cyber criminals are targeting third-party providers, who may deal with hundreds of websites, rather than attacking a website individually, exponentially increasing the damage inflicted.


