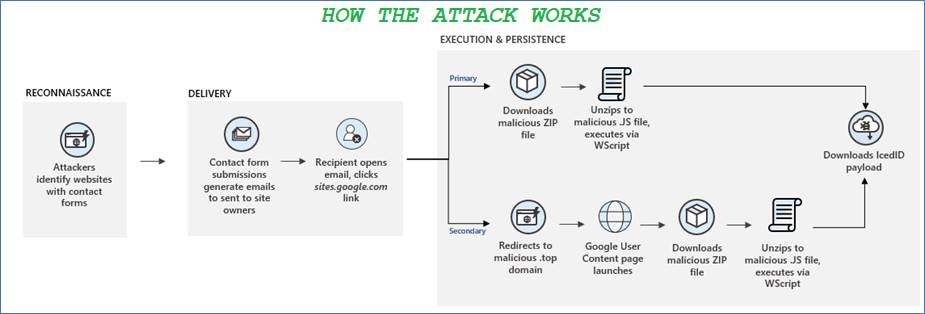
Earlier this month, Microsoft threat analysts released an alert in a blog post warning organisations of a new attack vector being used to deploy malware.
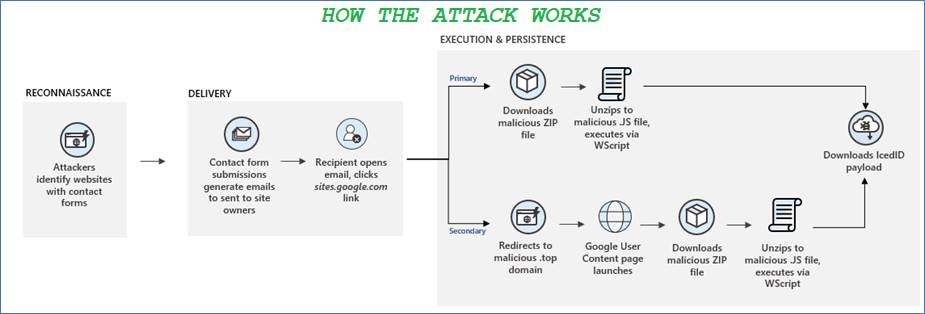
Earlier this month, Microsoft threat analysts released an alert in a blog post warning organisations of a new attack vector being used to deploy malware.
Gardaí have reported a sharp increase in the number of invoice redirect and CEO fraud-style attacks on Irish businesses in the last few months. “We are getting a couple of cases every week now”, according to Detective Superintendent Pat Lordan, who said that both small and large companies are being hit for amounts ranging from €10,000 into the millions.
In a global sting, named Operation reWired, authorities in the US and around the world have arrested 281 individuals that were involved in a global Business Email Compromise (BEC) scam. The ring had been under investigation for months, during which they were found to have hijacked email accounts belonging to company executives, impersonated staff and ultimately tricked unsuspecting employees into wiring millions in funds into the group’s accounts.

The cryptocurrency saga continues. A malicious extension has been removed from Google’s Chrome browser after it was revealed that it had been spreading through Facebook, attempting to steal passwords from unsuspecting users and taking advantage of their PCs to mine cryptocurrency. This isn’t the first time that cyber criminals have attempted to hijack other people’s computers in order to mine cryptocurrency for them. The extension, named FacexWorm, used Facebook messenger to spread to other users, sending what appears to be a Youtube link, which actually redirected the user to a fake landing page. The extension then communicated with criminal servers in order to download further malicious code onto the user’s PC.

It’s been a bad year for Facebook so far. They recently revealed that they may have improperly shared the details of 87 million users with a third-party, the now-infamous political consulting firm Cambridge Analytica. Then, on Wednesday, Mark Zuckerberg himself admitted during a press conference that “malicious actors” may have took advantage of Facebook to obtain the public data of all or most of Facebook’s 2.2 billion strong user base.
