It’s 2018, and cyber crime is on the rise. It seems every other week there is another data breach or cyber attack somewhere in the world, and many people are rightfully apprehensive that they may be hacked too, or even that their details may have been exposed online through a breach of a service that they use. What if your email and password were compromised in the Adobe breach in 2013, the Yahoo breach in 2016, or the LinkedIn breach in 2012? What if your email had been obtained online and sold to cyber criminals as part of a spam list, such as Exploit.In, or the Anti Public Combo List, both discovered in 2016? If so, you may be at risk of hackers gaining access to your accounts, or even committing identity fraud against you. Luckily, security researcher and Microsoft regional director Troy Hunt has developed a database so that you can check to see if you’ve been compromised – so you can secure your online presence again.
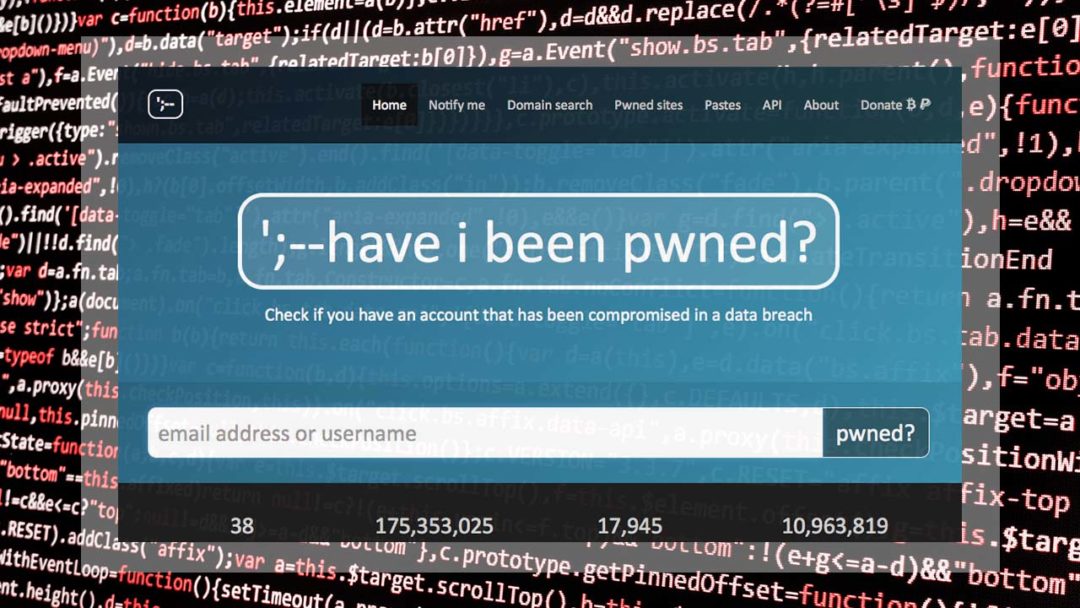
haveibeenpwned.com is a breach database run by security researcher and Microsoft regional director Troy Hunt
The website in question is haveibeenpwned.com, created as a free resource for users around the world to quickly check if their credentials have been compromised online. It’s simple and free to use, allowing anyone to enter their email address – which is then checked against a database of known hacks and breaches – and it tells you if you’ve been caught up in any of them.
This is particularly important due to a tactic called credential stuffing, where a cyber criminals gains access to your email and password for one service and proceeds to try that same combo on as many other websites as they can, to see if you have reused that password anywhere. Imagine your Adobe account was hacked, and you used the same password for another account such as your PayPal. It would only be a matter of time before someone who had access to the breached data realised that they could get into your PayPal account, even if you had changed your password for Adobe upon hearing about the initial breach.
Cyber criminals can be quite smart and surprisingly collaborative, pooling their knowledge of breached user accounts together in order to better gain illegitimate access to them. For example, several spam/breach combo lists have been compiled, which take data from various breach sources and pieces them together, often selling the data online on the dark web.
Now, what do you do if you do find that your business or personal email has been compromised in a breach? First off, you need to change your password for the service in question if you haven’t already changed it since the breach occurred. Then, you need to think about any other services you may have used that password for and change it there as well. And then, crucially, you should never use that password again.
When it comes to creating passwords, it’s important that each website or service you use has its own unique password, to avoid credential stuffing attacks against you in the future, when (not if) another breach occurs. We would advise using a password manager to generate and store your passwords for you – LastPass and Dashlane are popular and secure choices.
Another step that we would advise taking is enabling multi-factor authentication where possible on all your online accounts, especially sensitive ones such as email, payments services, and social media. Your email is key to resetting passwords to many of your other services, so it’s crucial that this one is protected particularly strongly. Payment services, obviously, can lead to loss of money if hacked, but be careful about your Facebook and other social accounts as well – you don’t want cyber criminals building up a detailed profile of you and your data, as this can lead to identity fraud.
For businesses, data obtained in such breaches can be particularly troublesome, as cyber criminals can use this information to launch spear-phishing attacks against your organisation, or even attempt to commit CEO fraud. We would advise checking your staff’s business emails against databases such as haveibeenpwned, and for those who use Active Directory, we would advise checking user passwords against known breach databases to ensure none of them have been previously compromised. This is something the new NIST password guidelines now recommend businesses implement, replacing the original NIST industry standard password security guidelines. Get in touch if you are not sure how to analyse large sets of user passwords or email addresses against data from previous data breaches.
Lastly, the greatest key in the fight against cyber crime is education. Anyone who uses the internet should have a basic grounding in security awareness, safe web browsing practices, and be able to recognise phishing emails and other signs of malicious activity online – and keep educated as threats change, so you don’t get caught out. Many (if not most) users fail to do the above steps, and for a business, that lack of education can prove critical, especially as phishing has been shown to be the main attack vector for nasty ransomware. Due to this, the industry standard (which is also mandated by the GDPR) is for organisations to train and even phish their own users on an ongoing basis. The time to take action is now!
