Ireland is claimed to be wide open to attacks from cyber criminals and rogue states, following an incident in which over 4000 websites around the world were hacked and used to mine crypto-currency. First reported by The Register, the breach affected the Department of Argicultures, Dublin City Council and Fingal, Cork, Wexford and Offaly county councils, and it is suspected to have also affected the websites of the Oireachtas, the Broadcasting Authority of Ireland, Women’s Aid and the Central Remedial Clinic. The crypto-mining attack was not limited to Irish websites, however, as the Information Commisioner’s Office in the UK, the United States courts and many more sites belonging to governments and organisations were also hit.
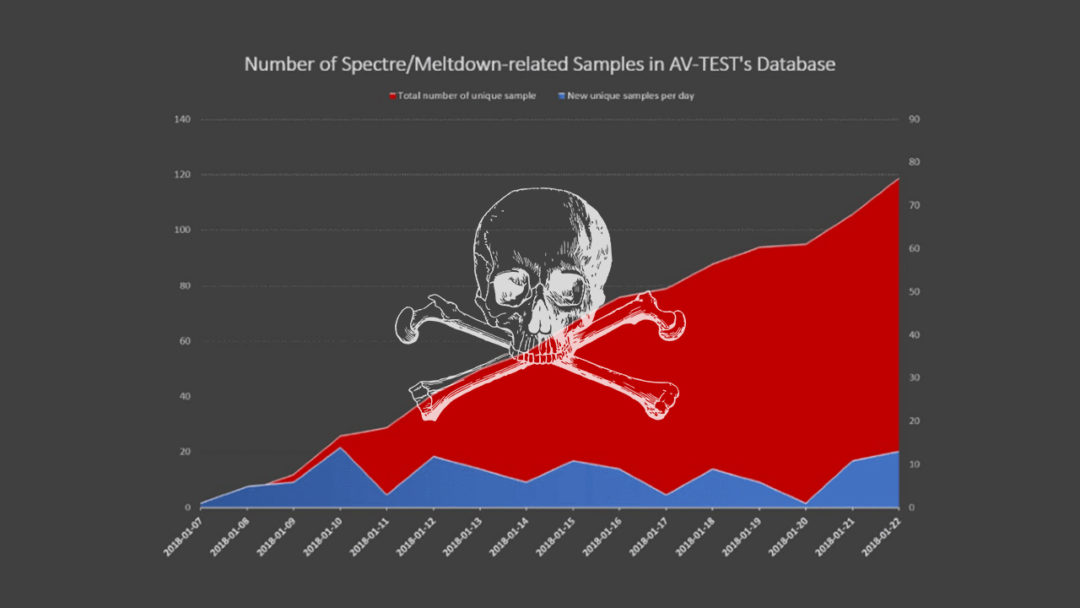
Antivirus Experts Discover Malware Samples Designed to Exploit Meltdown and Spectre
It looks like the Meltdown and Spectre fiasco is only just getting warmed up. Security researchers at antivirus testing firm AV-TEST have discovered more than 130 samples of malware that attempts to leverage the Meltdown and Spectre vulnerabilities. The malware samples analysed by AV-TEST appear to be mostly Poof-of-Concept code, and still in the research phase, however, it is believed that cyber criminals will be similarly experimenting with malware that utilises these vulnerabilities.
Meltdown and Spectre will haunt IT systems for years to come, potentially, as between them they can affect most processors in use since 1995
Defcon 1 – Critical Meltdown and Spectre Bugs Means Billions of Intel Devices Easily Hackable
2018 certainly knows how to make an entrance. The Christmas turkey has barely been finished and we’re told that nearly every electronic device on the planet with an Intel processor (from servers to PCs, smart devices and more) are susceptible to not one, but possibly two of the worst critical hardware related flaws ever known (Meltdown & Spectre). Flaws that can allow a hacker to steal your data without a hint of detection. In cases like these we often hear “but I have the latest next generation antivirus software”, but it’s not going to help you here I’m afraid. “And I have the latest next generation firewall and a state of the art SIEM solution just installed” – no good for fixing this either. You may even be really good and have your staff trained in security awareness and your systems backed up offsite – but unfortunately neither will address the root cause of this global issue. Even Santa couldn’t help fix this one – that’s how serious this is.
Meltdown and Spectre could be the worst ever bugs to hit electronic devices, making them easily hackable.
The hardware flaws have been aptly named “Meltdown” and “Spectre”. They sound like something straight out of a James Bond spy movie – and to be honest – the names aren’t far off, given if exploited, spying on you is exactly what a hacker could do. Predictions have already come in from experts that this could be the biggest disaster in IT history, and similar to the KRACK WiFi vulnerability of last year, Meltdown and Spectre could take years to fully fix. While important workarounds are available in some cases and must be put in place (see below) , only a hardware redesign in processor architecture will truly lay these bugs to rest.
To make matters worse, now that the crafty hackers know about it and with the EU GDPR data protection regulation coming into force on the 25th May – we predict, this year is going to see some considerable cyber-attacks that will try to take advantage of at least one of these flaws which may result in some pretty serious data breaches and some serious GDPR related fines. Its time like these one would think “Why did we ever go paperless?”.
Macro Malware: A Common Weapon for Phishing Attacks
A macro is a small piece of code that runs within a software program such as Microsoft Word or Excel, and is normally used to automate common or repetitive tasks. Macro malware is the practice of hiding a virus in a macro code and enticing unsuspecting users into downloading a Word or Excel file and running the macro script within, which then will download a virus, malware or even ransomware onto that person’s PC. Macro malware was common during the 1990s, but lapsed in popularity through most of the 21st century as increasingly savvy PC users learned how to spot the spam or phishing emails that delivered them, which were often riddled with typos. Nowadays, however, macro malware is seeing a big return due to two factors – Phishing emails are becoming increasingly sophisticated and no longer have obvious typos in them, and ransomware – a very profitable form of malware for criminals – can be easily downloaded via a macro, leading to entire networks being encrypted and held to ransom. It is now critical that all users understand the threats that macro malware can pose, particularly to their organisation, and learn how to spot the attacks before it’s too late.
Excel files are a common means of transmission for macro malware, which can download ransomware to infect entire networks at a time
KRACK – The Vulnerability That Affects Nearly Every Wi-Fi Device on the Planet
On Monday, it was announced publicly that Wi-Fi security, specifically the WPA2 standard, was essentially broken. The culprit is a bug named KRACK (Key Reinstallation Attack) which takes advantage of fundamental flaws in how WPA2 operates, and has exposed many shortcomings in how the industry responds to such attacks as well. WPA2 (Wi-Fi Protected Access II) is hugely prevalent, as it is the current generation of authentication used on wireless networks. That means that almost every wireless device could be affected by KRACK, as most devices use WPA2. This includes everything from laptops and phones to routers and IoT (Internet of Things)/Smart devices.


