The cryptocurrency saga continues. A malicious extension has been removed from Google’s Chrome browser after it was revealed that it had been spreading through Facebook, attempting to steal passwords from unsuspecting users and taking advantage of their PCs to mine cryptocurrency. This isn’t the first time that cyber criminals have attempted to hijack other people’s computers in order to mine cryptocurrency for them. The extension, named FacexWorm, used Facebook messenger to spread to other users, sending what appears to be a Youtube link, which actually redirected the user to a fake landing page. The extension then communicated with criminal servers in order to download further malicious code onto the user’s PC.
Website Offering DDoS Cyber Attacks For Just €12 Taken Down by Police
The ongoing battle between cyber criminals and cyber security forces rages on, as one of the world’s largest DDoS-for-Hire websites has been taken down by Dutch police. The website was the target of Operation Power OFF, a coordinated effort by police from the Netherlands, UK, Spain, Croatia, Canada, US, Germany, Europol and several other countries. The site in question, webstresser.org, was believed to have been responsible for attacks against several of the UK’s largest banks in November 2017, as well as carrying out attacks on government websites and police forces around the world. DDoS, or Distributed-Denial-of-Service, is an attack where many online devices (such as PCs or IoT devices) are used to overwhelm a website or online service with traffic, essentially forcing them to freeze up or shut down.
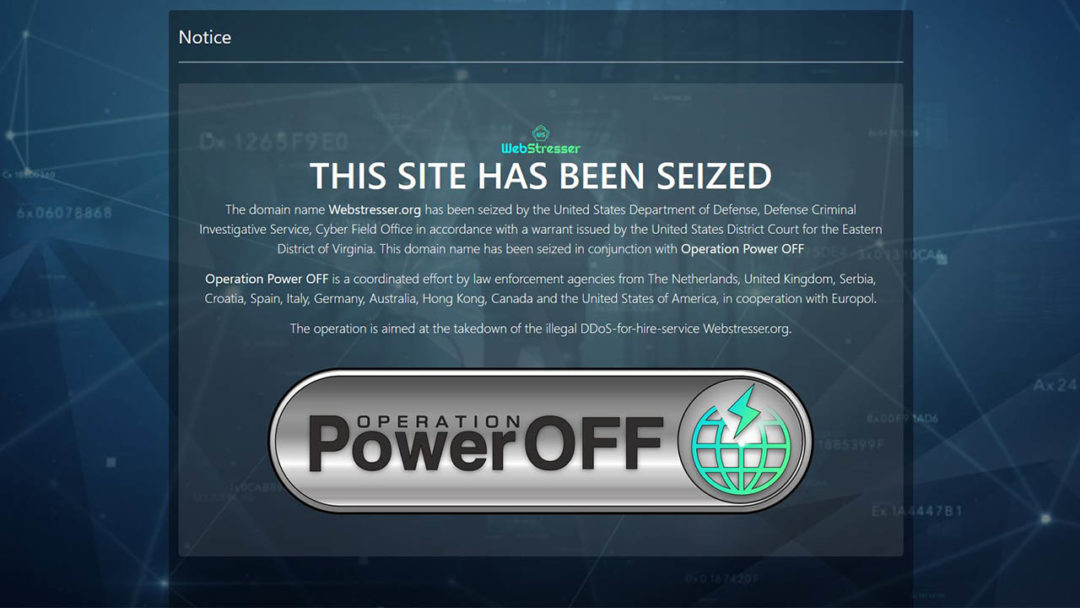
Webstresser.org, the largest known DDoS-for-Hire site, was seized by Operation Power OFF, a coordinated effort from cyber police from a dozen countries.
Small Businesses Experiencing More Cyber Attacks Than Large Organisations
We’ve all seen the headlines when a large multi-national corporation suffers a data breach, but are small businesses able to ‘fly under the radar’ for cyber crime? Well, according to Verizon’s annual data breach incident report, the opposite may be the case. While large organisations make headlines, the report found that 58% of data breaches actually occurred in small and medium-sized companies.
“Many small businesses don’t have the resources focused on security and training, and employees are not cognizant of being at risk,” according to the Vice President of Experian Data Breach Resolution, Michael Bruemmer. “Some of these businesses, especially startups, may have no or small revenue, but they may be processing credit cards or holding personal data for other companies, and they don’t realize they have to protect it.”

Half of all cyber attacks are currently believed to target small businesses (Source: Verizon Annual Data Breach Report)
Meltdown and Spectre Attacks Expected to Surge in 2018
The world has not seen the last of Meltdown and Spectre, according to a recent report by cyber security and firewall specialists SonicWall. By January 2018, the company had already come across 500 ‘zero day’ malware programs designed to take advantage of various processor vulnerabilities. On Meltdown and Spectre, SonicWall has said, “It’s likely these are just two of many processor vulnerabilities already in play. We predict the emergence of password stealers and infostealers to take advantage of Meltdown and Spectre vulnerabilities”.
Meltdown and Spectre are just two CPU vulnerabilities among many that criminals are expected to continue exploiting throughout 2018 and beyond.
World’s Largest DDoS Attack Record Broken Twice in a Week
In a worrying new cyber threat trend, the record for largest DDoS (Distributed Denial of Services) attack has been broken, not once, but twice, over the past week. A DDoS attack, in essence, is an attempt to make an online service (such as your business’s website) unavailable by overwhelming it with traffic from various sources. Last week, the coding repository GitHub was briefly taken offline in a 1.3 Terrabits-per-second DDoS attack. This wasn’t entirely unsurprising, as DDoS attacks have been steadily building throughout 2018, but March has definitely been the worst month so far. Now, an unnamed US service provider has reported experiencing an even larger DDoS attack, which hit 1.7 Terrabits-per-second, only a few days after the previous record had been broken. This could pose a significant threat for many businesses that operate memcached database servers, which typically have high-bandwidth access and can be badly impacted by DDoS attacks.


