Cyber criminals have always targeted users, finding it easier to trick unsuspecting employees than to bypass complex technical security measures – and this trend has been growing steadily the last few years. Identify fraud, where criminals impersonate someone else in order to steal their money or use their account to manipulate others, is now one of the most common types of cyber crime there is. Account takeover attacks, where criminals gain access to a user’s account and use it to send spam or phishing emails, is also on the rise, often allowing malicious emails to bypass email security filters.
Irish Companies Reporting Less Than 5% of Cyber Crime
Irish companies are believed to be reporting less than 5% of cyber attacks to police, according to disparities between figure from the Garda cyber crime unit and reports from private cyber security companies. Detective Superintendent and Head of the Garda Nation Cyber Crime Bureau, Michael Gubbins, has said that brand damage and embarrassment are among reasons given by companies for the under-reporting of cyber crime to the Gardai.

Gardai believe that companies are afraid of brand damage, leading to a vast under-reporting of cyber crime to authorities.
Eir Loses Unencrypted Laptop Containing 37,000 Customers’ Details
Eir is back in hot water again with the Data Protection Commissioner after the company issued a statement stating that it had lost an unencrypted staff laptop containing the details of 37,000 Eir customers. Eir has said that the data contained names, email addresses and customer account number, but that no financial details were compromised in the breach.

Eir is no stranger to data breaches, and has reported having multiple laptops with customer data lost or stolen in the past
Ransomware Strain ‘SamSam’ Reportedly Earned Handlers Over €5.1m
A strain of ransomware titled SamSam has earned its handlers over 5.1 million euros to date, according to estimates, since it first began hitting enterprises in 2015. Security firm Sophos has released the data in a report, after tracking the Bitcoin addresses found on SamSam ransom notes and sample files.
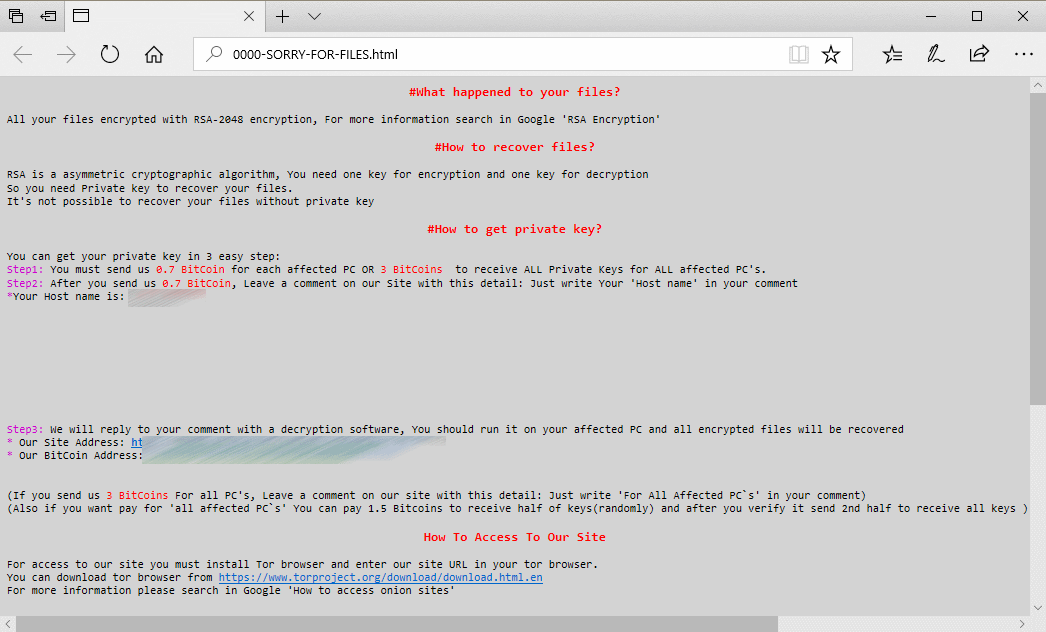
The note displayed on PCs that were infected by SamSam ransomware, as seen by businesses, hospitals, schools, local councils and more
Enterprise Resource Planning Applications Next Big Cyber Attack Target
Cyber criminals are beginning to target Enterprise Resource Planning (ERP) applications, with the aim of disrupting and stealing data from large companies, according to reports from both security experts and the US government. According to a recent report from security companies Digital Shadows and Onapsis, hacktivists and state-sponsored groups in particular and looking to exploit flaws in platforms provided by Oracle and SAP.