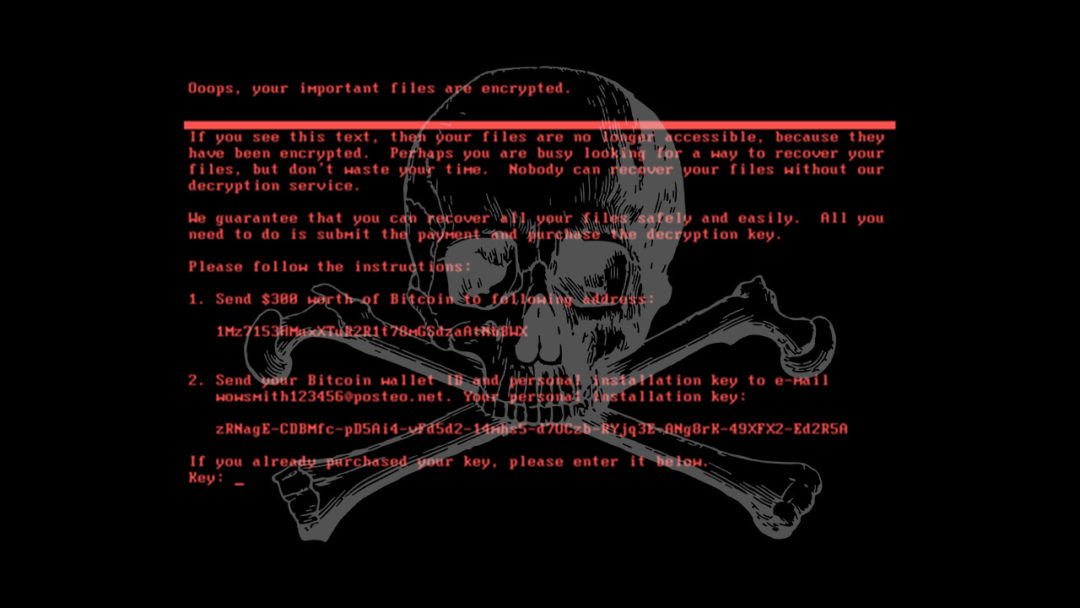
The governments of the UK, US, Australia and more have publicly blamed Russia for the NotPetya ransomware attacks, which crippled businesses all over Europe back in June 2017 with a particularly nasty and destructive strain of ransomware. Last Thursday, the White House press secretary Sarah Sanders stated that NotPetya was “a reckless and indiscriminate cyber-attack that will be met with international consequences”, squarely blaming the Russuan Military and the Kremlin for causing billions of dollars’ worth of damage to businesses and states alike. The same day, the British defence secretary Gavin Williamson accused the Russian government of “undermining democracy”, after the attack, which was primarily aimed at the Ukraine, spread uncontrolled throughout Europe and beyond and caused major disruption to commerce and public services.
HSE, Dublin County Council, Department of Argiculture and More Hit by Crypto-Mining Cyber Attack
Ireland is claimed to be wide open to attacks from cyber criminals and rogue states, following an incident in which over 4000 websites around the world were hacked and used to mine crypto-currency. First reported by The Register, the breach affected the Department of Argicultures, Dublin City Council and Fingal, Cork, Wexford and Offaly county councils, and it is suspected to have also affected the websites of the Oireachtas, the Broadcasting Authority of Ireland, Women’s Aid and the Central Remedial Clinic. The crypto-mining attack was not limited to Irish websites, however, as the Information Commisioner’s Office in the UK, the United States courts and many more sites belonging to governments and organisations were also hit.

Over 4000 websites around the world were affected in the crypto-mining attack, many of which belonged to government organisations
Carphone Warehouse Fined €450,000 Over Data Breach and “Significant Inadequacies”
Carphone Warehouse have been ordered to pay a fine of £400,000 (over €450,000) to the UK Information Commissioner’s Office, one of the largest fines the ICO has ever issued to a company. A data breach at Carphone Warehouse occurred in 2015, which subsequently led the ICO to investigate the company and discovered a series of “systematic failures” in security practice. The severity of the fine reflected the fact that up to 3 million customers’ data was compromised, in addition to the data of a further 1000 employees. The data itself was also considered extensive by the ICO, as names, addresses, phone numbers, marital status and dates of birth were all leaked. It is further believed that some 18,000 customers had payment card details leaked as well.

The £400,000 fine issued to Carphone Warehouse was one of the largest issued by the ICO. Over 3 million records were compromised in the breach.
Morrisons Ruled Responsible for Data Leaked by Staff Member
In a case that has set a new precedent in data breach law, UK supermarket giant Morrisons has been found liable by a High Court for the actions of a former staff member who purposely leaked payroll data for thousands of employees. The decision was reached as part of a class-action lawsuit brought against Morrisons by over 5000 current and past employees of the company, and was in relation to an incident that took place in 2004 – where an employee posted 100,000 employees’ personal details on the internet. This personal information included bank details, salary, insurance information, phone numbers and addresses. Lawyers have refereed to this ruling as a “landmark” decision, as it was the first class-action suit filed over a data breach in the UK, and ruled that Morrisons was liable to owe compensation to the victims despite the judge ruling that Morrisons had not been at fault in any way. However, this case is very much in keeping with current trends in regulation to fiercely protect user data, and the high expectations being placed to companies to ensure this.
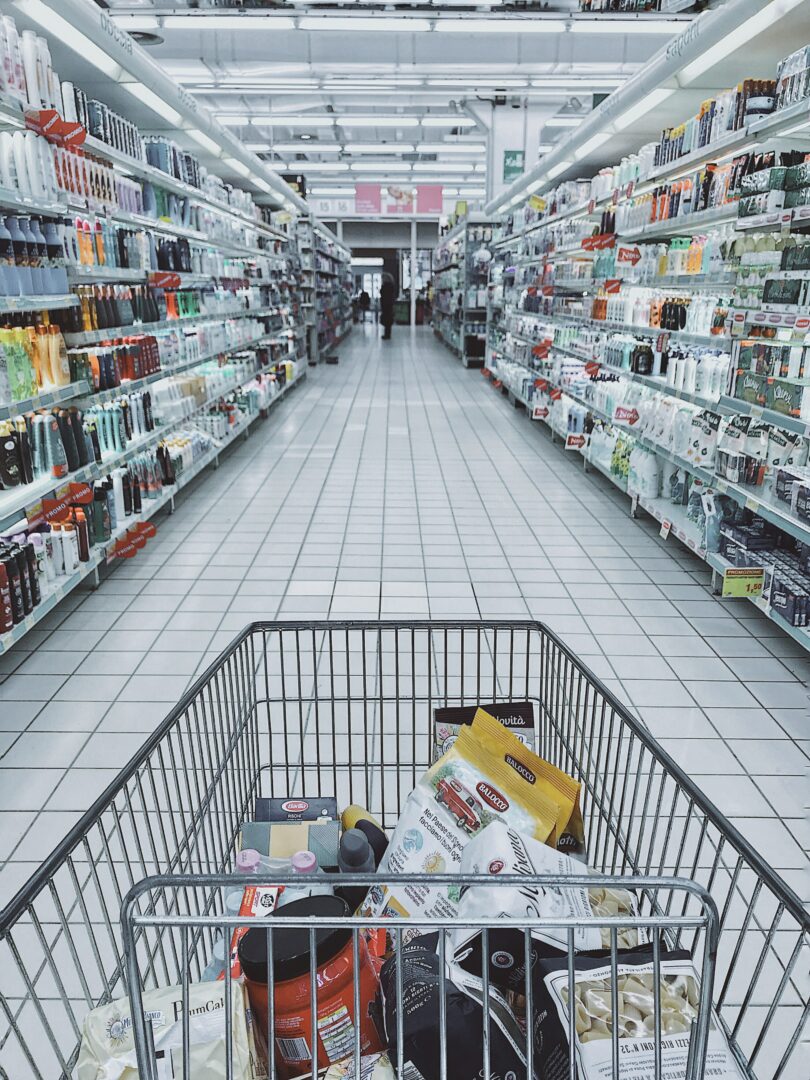
The High Court decided in a landmark ruling that Morrisons must compensate the victims of the data breach, despite not being at fault
Central Statistics Office P45 Data Breach Caused by Human Error
The Central Statistics Office has admitted to a data breach involving an error by a staff member, leading to a sever breach of data protection rules. Reports were made last week that a past employee for the CSO has been sent P45s of other past and present employees in error. The past employee was outraged at the time, as she believed that 1000 people’s records had been breached.
The CSO has since issued a “sincere apology” for the incident, and volunteered that the incident had not affected 1000 people, but had actually concerned 3000 former employees.