Train staff, install Next Generation security and disable macros as the latest fileless malware exploits a lack of all three to steal data.
I’m afraid to say but gone are the days when just having standard security such as Anti-virus software was enough. Cybercriminals are now using complex clandestine techniques to exploit standard system tools and protocols that are not always monitored.
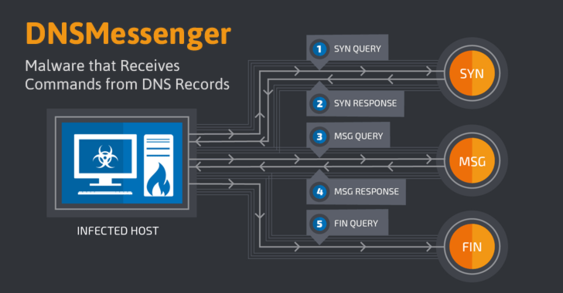
The latest example of such attack is DNSMessenger – a new Remote Access Trojan (RAT) that uses DNS queries to conduct malicious PowerShell commands on compromised computers – a technique that makes the RAT difficult to detect onto targeted systems. Just like their physical counterparts, without a trap in place (i.e a next generation security detection system) they won’t be caught and will end up causing untold damage.
Read on for what next generation security you need to protect your business from these advanced next generation threats.
The Trojan came to the attention of Cisco’s Talos threat research group by a security researcher named Simpo.
DNSMessenger Attack Is Completely Fileless
Analysis of the malware led Talos researchers to discover a sophisticated attack comprising a malicious Word document and a PowerShell backdoor. The backdoor was found to be communicating with its command-and-control servers sending covert information via DNS requests.
Distributed through an email phishing campaign, the DNSMessenger attack is completely Fileless, as it does not involve writing files to the targeted system; instead, it uses DNS TXT messaging capabilities to fetch malicious PowerShell commands stored remotely as DNS TXT records.
This feature makes it invisible to standard anti-malware defenses.
PowerShell is a powerful scripting language built into Windows that allows for the automation of system administration tasks.
DNSMessenger Attacks Via Email Phishing Campaign

If the victim has local administrative access, it allows the malware to stay persistent on the system even after a reboot.
The DNSMessenger malware uses DNS TXT records that, by definition, allows a DNS server to attach unformatted text to a response. In this regard data from users machines can be covertly transferred to the hackers command and control centers. This script queries the command-and-control servers via DNS TXT message requests to ask what commands to execute. Any command received is then executed, and the output is communicated back to the C&C server, allowing the attacker to execute any Windows or application commands on the infected system.
“This malware sample is an excellent example of the length attackers are willing to go to stay undetected while operating within the environments that they are targeting,” the Talos researchers said.
“It also illustrates the importance that in addition to inspecting and filtering network protocols such as HTTP/HTTPS, SMTP/POP3, etc. DNS traffic within corporate networks should also be considered a channel that an attacker can use to implement a fully functional, bidirectional C2 infrastructure.”
This is not the first time when the researchers came across a Fileless malware. As we reported last month, Kaspersky researchers also discovered fileless malware, that resides solely in the memory of the compromised computers, targeting banks, telecommunication companies, and government organizations in 40 countries.
What Next Generation Security Do I Need?
The once popular commonplace IT security solutions are quickly becoming defunct as the cyber criminals exploit weaknesses which they no longer monitor for or protect you against.
Next generation security solutions are slowly becoming more commonplace as users and businesses become more educated on what is quickly becoming the new standard in IT Security.
Below we have listed some are a list of some of the most important next generation security layers you can put in place to help protect your business.
- Security Awareness Training and Testing For Staff – Firstly, ensure you and your staff undertake ongoing IT and Cyber security awareness training so they can identify covert email phishing attacks such as this one before email links or attachments are clicked. Then test your staff regularly with simulated email phishing campaigns mimicking the latest scams to trick users and keep them on their toes.
- Next Generation Anti-virus – Replace your existing Antivirus (AV) with Next Generation AV software that can detect fileless malware the resides in memory rather than a specific file on your hard drive that standard Anti-virus software would scan for.
- Next Generation DNS Filtering – DNS filtering can scan DNS traffic and block the covert transfer of sensitive data through the malicious exploitation of the DNS protocols.
- Advanced Threat Protection – An ATP email security solution scans and tests these email threats/attachments in a safe cloud based sandbox, before they reach your inbox or are downloaded to your network.
- Next Generation Firewall – Next Generation Firewalls are fast becoming a required layer of defense against similar threats and will also bolster your protection against such threats, especially those that include ATP.
- Disable Macros in Word & Excel – Ensure your Microsoft Office Word and Excel macros are disabled across the network.
- Backup & Test Recovery – Last but not least – ensure you have all your critical data, emails, applications and databases backed up locally and offsite. Ensure your backups are tested regularly so you can recover your data and continue operations should the worst happen.
Remember security is a layered approach. It’s best to think of IT Security like the layers of an onion. Every layer adds another line of defense to protecting what matters most to your business “your data”.
Need help with putting in place some or all of the above. Contact us today for more information on our comprehensive Next Generation IT security and Cyber Security services.
Tech Guard – “We do the research so you don’t have to.”
Source: The Hacker News
