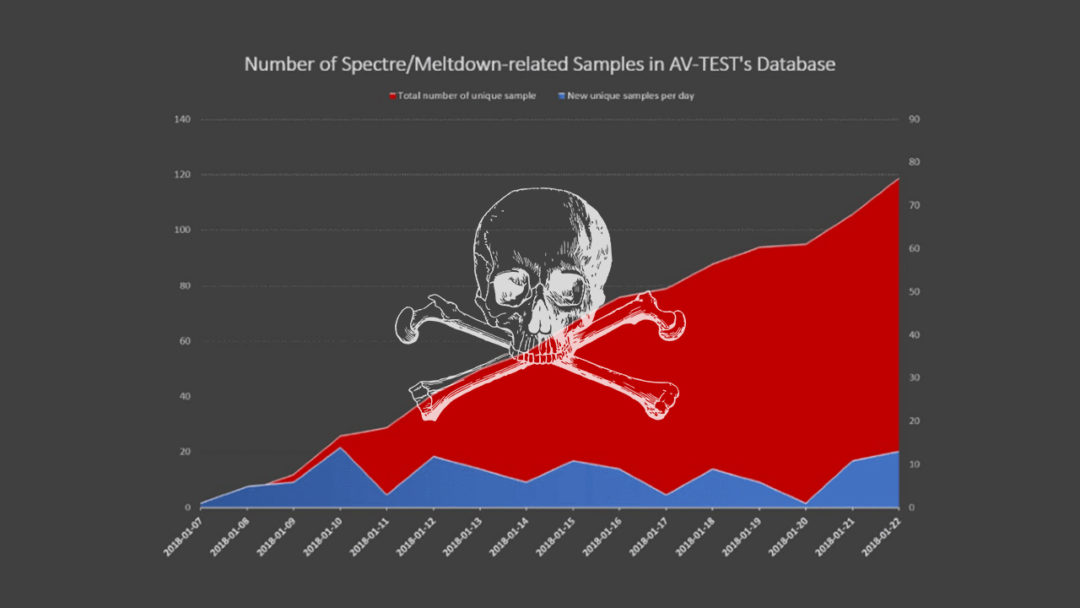
It looks like the Meltdown and Spectre fiasco is only just getting warmed up. Security researchers at antivirus testing firm AV-TEST have discovered more than 130 samples of malware that attempts to leverage the Meltdown and Spectre vulnerabilities. The malware samples analysed by AV-TEST appear to be mostly Poof-of-Concept code, and still in the research phase, however, it is believed that cyber criminals will be similarly experimenting with malware that utilises these vulnerabilities.
Reports Show Cyber Crime Cost Consumers €150bn in 2017
Norton has just released their annual Cyber Security Insights Report, which analyses the effects of cyber crime around the world. One of the key findings of this report is that when it comes to cyber security, “consumers are overconfident in their security prowess, leaving them vulnerable and enabling cyber criminals to up the ante this year, which has resulted in record attacks”. Over the course of 2017, the report estimates that over 978 million adults in 20 countries around the world experienced cyber crime. These attacks cost consumers an estimated €150 billion.
While most people stated that cyber security was important to them, one third of people stored their passwords insecurely and one fifth admitted to using the same password across all sites they use. Over half of the respondents reported either they or someone they knew had been a victim of cyber crime, with the average cyber crime victim spending almost three full working days recovering from the attack.

“When it comes to cyber security, consumers are overconfident in their security prowess, leaving them vulnerable and enabling cyber criminals to up the ante this year, which has resulted in record attacks.”
Defcon 1 – Critical Meltdown and Spectre Bugs Means Billions of Intel Devices Easily Hackable
2018 certainly knows how to make an entrance. The Christmas turkey has barely been finished and we’re told that nearly every electronic device on the planet with an Intel processor (from servers to PCs, smart devices and more) are susceptible to not one, but possibly two of the worst critical hardware related flaws ever known (Meltdown & Spectre). Flaws that can allow a hacker to steal your data without a hint of detection. In cases like these we often hear “but I have the latest next generation antivirus software”, but it’s not going to help you here I’m afraid. “And I have the latest next generation firewall and a state of the art SIEM solution just installed” – no good for fixing this either. You may even be really good and have your staff trained in security awareness and your systems backed up offsite – but unfortunately neither will address the root cause of this global issue. Even Santa couldn’t help fix this one – that’s how serious this is.
Meltdown and Spectre could be the worst ever bugs to hit electronic devices, making them easily hackable.
The hardware flaws have been aptly named “Meltdown” and “Spectre”. They sound like something straight out of a James Bond spy movie – and to be honest – the names aren’t far off, given if exploited, spying on you is exactly what a hacker could do. Predictions have already come in from experts that this could be the biggest disaster in IT history, and similar to the KRACK WiFi vulnerability of last year, Meltdown and Spectre could take years to fully fix. While important workarounds are available in some cases and must be put in place (see below) , only a hardware redesign in processor architecture will truly lay these bugs to rest.
To make matters worse, now that the crafty hackers know about it and with the EU GDPR data protection regulation coming into force on the 25th May – we predict, this year is going to see some considerable cyber-attacks that will try to take advantage of at least one of these flaws which may result in some pretty serious data breaches and some serious GDPR related fines. Its time like these one would think “Why did we ever go paperless?”.
Dublin Zoo Hit by Cyber Criminals for €500,000
Dublin Zoo has admitted it has been hit by a scam in which cyber criminals were reportedly able to steal up to €500,000. The zoo has stated that they are cooperating with the Garda National Economic Crime Bureau in a case of invoice redirect fraud. While neither the Gardaí nor Dublin Zoo revealed the amount of money taken, sources have reported that it was up to €500,000, most of which was successfully recovered.

Reports indicate that Dublin Zoo may have lost up to €500,000 through the scam, with an estimated €130,000 remaining at large overseas.
Password Sharing “Standard Practice” Among British MPs
Nadine Dorries, a British MP, has made news over the past few weeks after admitting on Twitter that she shares the password to her work PC with other staff in her office and even “interns on exchange programs”. According to Dorries, the main reason for this is that her staff can access a shared mailbox on the PC and reply to constituents. More worrying still, in wake of the backlash directed at Dorries, other MPs have come forward and admitted to the practice, revealing a worrying trend. In a further statement that showed up Dorries’ lack of data protection savvy, she tweeted that since she was backbench MP without access to government documents, there was nothing sensitive to access. Dorries (and hopefully all other MPs sharing their passwords) are in for a rude awakening, however, as not only is sharing passwords against the rules of parliament in the UK, but even information as basic as an address book constitutes Personally Identifiable Information (PII) which is subject to strong protection under existing data protection laws – and will be protected even more fiercely under the upcoming GDPR, even in the UK.

 Password sharing may be standard practice among MPs, but it is far from best practice. Mailbox delegation could achieve the same productivity with a fraction of the risk.
Password sharing may be standard practice among MPs, but it is far from best practice. Mailbox delegation could achieve the same productivity with a fraction of the risk.