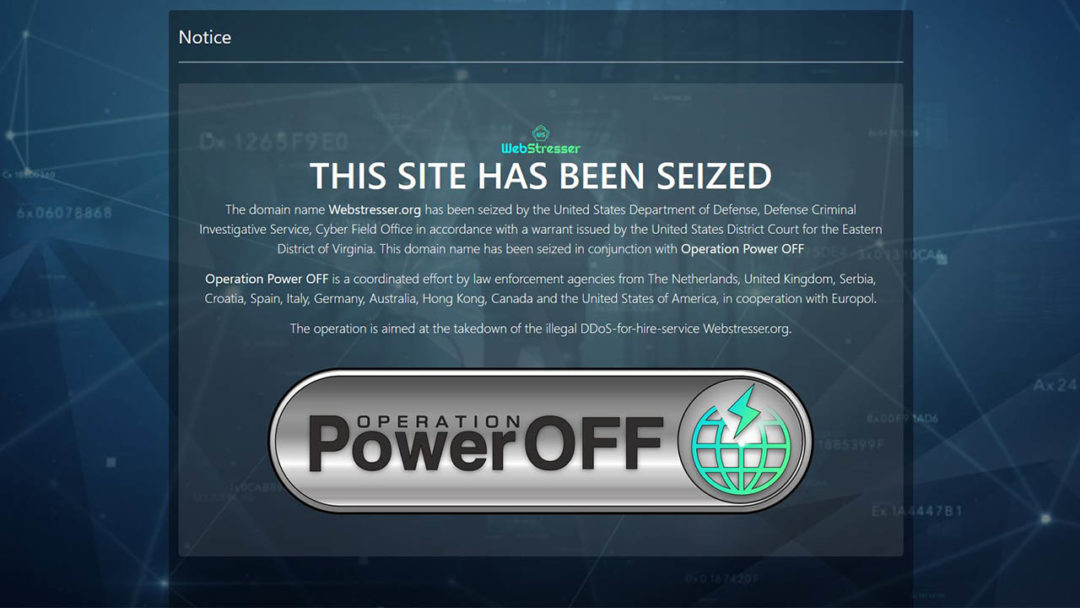
The ongoing battle between cyber criminals and cyber security forces rages on, as one of the world’s largest DDoS-for-Hire websites has been taken down by Dutch police. The website was the target of Operation Power OFF, a coordinated effort by police from the Netherlands, UK, Spain, Croatia, Canada, US, Germany, Europol and several other countries. The site in question, webstresser.org, was believed to have been responsible for attacks against several of the UK’s largest banks in November 2017, as well as carrying out attacks on government websites and police forces around the world. DDoS, or Distributed-Denial-of-Service, is an attack where many online devices (such as PCs or IoT devices) are used to overwhelm a website or online service with traffic, essentially forcing them to freeze up or shut down.
Small Businesses Experiencing More Cyber Attacks Than Large Organisations
We’ve all seen the headlines when a large multi-national corporation suffers a data breach, but are small businesses able to ‘fly under the radar’ for cyber crime? Well, according to Verizon’s annual data breach incident report, the opposite may be the case. While large organisations make headlines, the report found that 58% of data breaches actually occurred in small and medium-sized companies.
“Many small businesses don’t have the resources focused on security and training, and employees are not cognizant of being at risk,” according to the Vice President of Experian Data Breach Resolution, Michael Bruemmer. “Some of these businesses, especially startups, may have no or small revenue, but they may be processing credit cards or holding personal data for other companies, and they don’t realize they have to protect it.”

Half of all cyber attacks are currently believed to target small businesses (Source: Verizon Annual Data Breach Report)
Cyber Attacks Rarely Change Tactics, According to NSA
According to Dave Hogue, the technical director of the NSA’s Cybersecurity Threat Operations Center, the technology used to implement cyber attacks evolves over time but the tactics used to carry them out rarely changes. Hogue told the crowd at the CyberUK conference in Manchester, “Every day we’re battling a new cyber-threat, but the more that things change the more that they stay the same.”

Dave Hogue is the technical director of the NSA CTOC, and claims that they have not responded to any ‘zero-day’ cyber attacks in two years.
ALL 2.2 Billion Facebook Users May Be Open to Social Engineering Attacks
It’s been a bad year for Facebook so far. They recently revealed that they may have improperly shared the details of 87 million users with a third-party, the now-infamous political consulting firm Cambridge Analytica. Then, on Wednesday, Mark Zuckerberg himself admitted during a press conference that “malicious actors” may have took advantage of Facebook to obtain the public data of all or most of Facebook’s 2.2 billion strong user base.

Social Engineering is becoming a larger problem for businesses and consumers alike over the past years. So what does it mean if cyber criminals have access to your public data?
Meltdown and Spectre Attacks Expected to Surge in 2018
The world has not seen the last of Meltdown and Spectre, according to a recent report by cyber security and firewall specialists SonicWall. By January 2018, the company had already come across 500 ‘zero day’ malware programs designed to take advantage of various processor vulnerabilities. On Meltdown and Spectre, SonicWall has said, “It’s likely these are just two of many processor vulnerabilities already in play. We predict the emergence of password stealers and infostealers to take advantage of Meltdown and Spectre vulnerabilities”.